__________
#18 | Posted by oneironaut at 2024-04-11 05:49 PM
This is false, Podesta was victim of a phishing email, that's not "hacking". Seriously calling it a hack is hilariously uninformed.
NOT calling "phishing" / "spearphishing" a "hack" is seriously and hilariously uninformed.
Hacking is a wide range of techniques not limited to just phishing, but phishing is a widely used form of initial "social engineering" methods popularized by hacker Kevin Mitnick (RIP) to get information such as logins and passwords used to facilitate further hacking process - data exfiltration and/or planting further malware, such as worms, viruses or ransomware.
Phishing is only one of many initial digital hacking methods, just like there are many "debuts/openings" in the chess game - you don't get to start in the middle.
---
#23 | Posted by LampLighter at 2024-04-11 06:19 PM
It wasn't just a few aides that the hackers went after; it was an all-out blitz across the Democratic Party. They tried to compromise Clinton's inner circle and more than 130 party employees, supporters and contractors.
While U.S. intelligence agencies have concluded that Russia was behind the email thefts, the AP drew on forensic data to report Thursday that the hackers known as Fancy Bear were closely aligned with the interests of the Russian government.
DNC and Hillary's campaign were protected by cybersecurity company Crowdstrike. They initially identified breach as cyber attack by APT28, which was later confirmed by multiple firms and agencies.
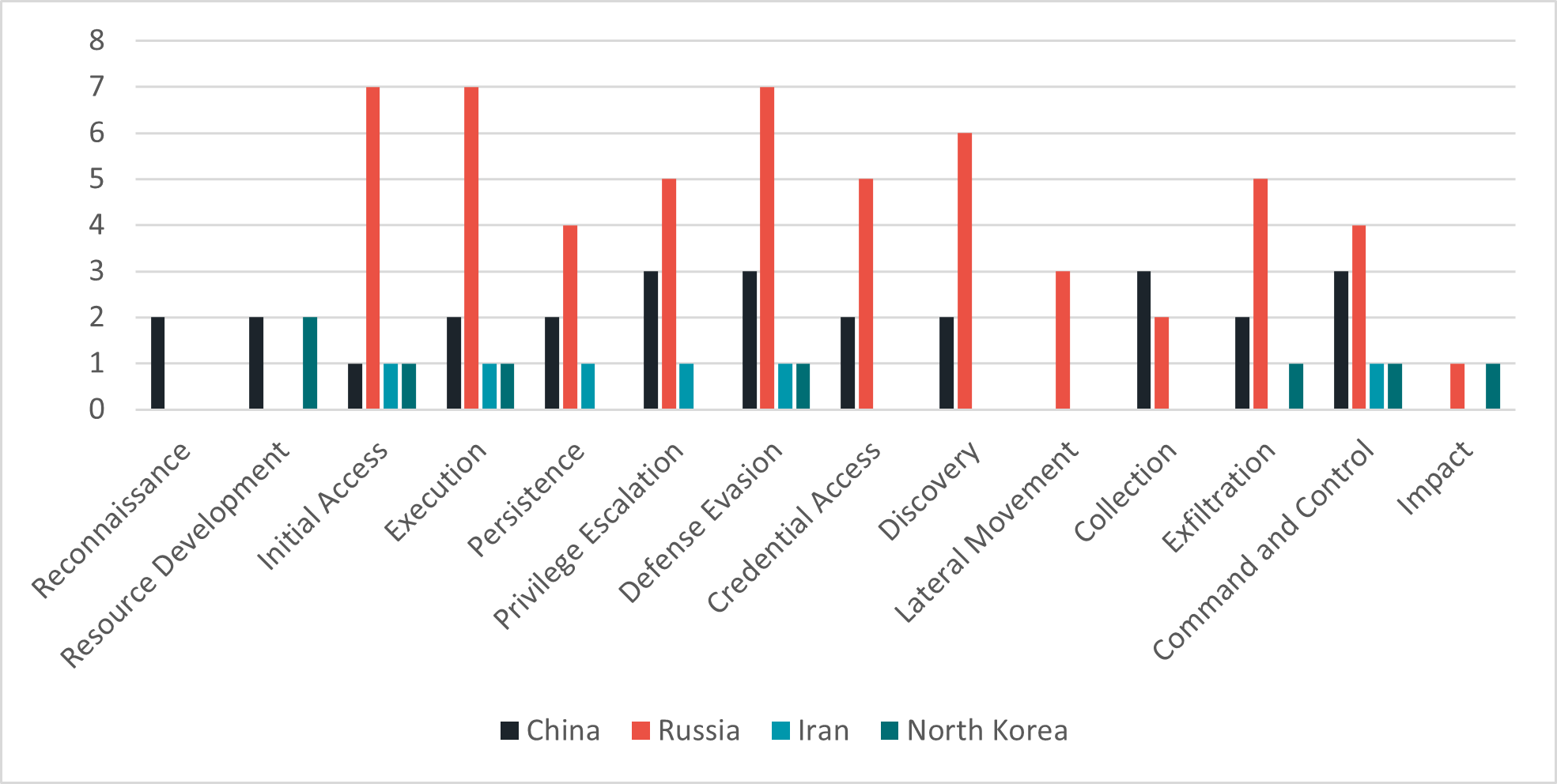
APT28 aka Fancy Bear, Tsar Team, Sofacy Group etc. are not just "closely aligned with the interests of the Russian government" - they are one of the Russian government's cyber espionage APT (Advanced Persistent Threat) teams, more specifically attached to and having all the resources of military intelligence unit / GRU. Other Russian government APTs are Cozy Bear aka Midnight Blizzard, Dark Halo etc (APT29, SVR and FSB) - which is responsible for recent, and still ongoing, breach and exfil of HPE and Microsoft's Azure/MS365-managed email accounts systems, including US and other governments accounts.
China has several APTs (e.g., APT20, APT27, APT30, APT31, APT41 etc.) as well as Iran (APT33, APT34 APT35) and North Korea (APT37), Pakistan etc. Israel's IDF Unit 8200 is one of the best at cyber warface, but works mostly to penetrate military targets, like Iran's nuclear arms facilities.
__________